Ah, she has served us very well. Let's talk about my first vision for lain.la and really get into the details on what the first version's goals were. I started lain.la because I needed an outlet from a personal event. Technology has always been that outlet. So I decided to build something. Anything. I started small in August 2020 - a website, then a Gitlab for projects, and a Pomf clone. More services expanded from there, such as VMs for friends and a Seedbox.
(You can see lain.la v1 in the bottom right corner here)

When I was planning this project, First and foremost, I needed to define what my targets were. I settled on these:
- VM only infrastructure with partially-enterprise hardware and software
- Templatable deployment methods
- Excellent performance per dollar
- Auto-healing in the event of network loss
- Power efficient
- Keep ne'er-do-well's off my home network
To meet all of these goals, I used a hybrid cloud approach. A VPS on Ramnode, tied via VPN to a beefy machine at home. The machine (A lovely Dell T5810 tower) cost barely a few hundred dollars at first, with these specs:
- E5-2678v3 CPU (12 cores, 2.5GHz)
- 32GB DDR4
- 120GB SSD (Boot)
- 1TB SSD (Data)
- 10TB iSCSI LUN (Bulk Data)
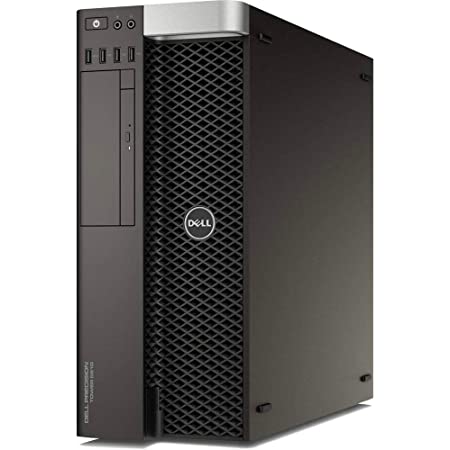
I then hooked this up via a single gigabit NIC and installed ESXi 7 (I have keys...) and we were off to the races. Later in the year, I upgraded to 64GB and 128GB of DDR4. The VPN part was handled via OpenVPN running on lain.la, and pfSense managing the OpenVPN connection on the host. A completely isolated virtual network handles VMs on 10.0.0.0/8, away from my 192.168.1.0/24 regular network. pfSense is the only machine in the network that has a connection to the uplink-less vSwitch AND a connection to the NIC. It is the gatekeeper of the VM network and encrypts all traffic before it ever leaves its grasp. This secures my home network.
I made a draw.io chart to illustrate how this worked, and I'll link that here now.
To describe what the hell all this above means, here is another bullet point list!
- A VM inside the red network is inside the 10.0.0.0/8 subnet. This is the protected network, isolated from my home network.
- Traffic destined to go outside that network passes through the vSwitch to the default gateway, pfSense, 10.0.0.1.
- pfSense encrypts all traffic outbound to head all the way out the Verizon FIOS gigabit fiber link I have to lain.la's OpenVPN server, 10.8.0.6.
- From there, it can get out to the world.
Incoming connections are a bit different.
- Data destined for a lain.la service can either go directly through a port OR via nginx reverse proxy. Either way, it travels back through the VPN, to 10.8.0.5, via masquerade OR nginx direct IP:port.
- pfSense has a NAT firewall table that maps the incoming requests to VMs and ports, exactly like port forwarding on a traditional router.
- The request is then passed to the VM on whatever the destination IP and port was.
This setup keeps my home network entirely seperate from the traffic. Entirely. Great for peace of mind. Downsides are that I have to do double NAT and be a port miser.